In today's digital world, network safety is paramount. Businesses of all scales are increasingly vulnerable to dangerous cyberattacks. This is where white hat hacking comes into play as a vital defense mechanism. Ethical hackers intentionally exploit vulnerabilities in systems before malicious actors can, effectively acting as your online protector.
- Through simulated attacks, ethical hackers provide valuable insights into the limitations of your systems.
- They then recommend remediation strategies to eliminate these vulnerabilities, strengthening your overall defense system.
Through investing in ethical hacking services, you can strategically protect your valuable resources and minimize the risk of a harmful cyberattack.
Need a Hacker? Ethical Solutions For Your Digital Fortress
In today's dynamic digital landscape, protecting your data is paramount. But what happens when you suspect a breach? Do you panic? Absolutely not! Instead, consider the strengthof ethical hacking. This isn't about unlawful intrusions; it's about proactively identifying weaknesses in your systems before malicious actors can capitalize them. Ethical hackers act as your digital bodyguards, meticulously assessing your networks and applications to fortify your defenses. By adopting ethical hacking practices, you can transform potential threats into opportunities for growth and enhanced security.
Navigating the Murky Waters of Hackers for Hire
In today's digital age, the line between ethical hacking and malicious cyber activity has become increasingly White hat blurred. Freelance security experts offer their skills to individuals and organizations alike, but navigating the legal and ethical implications of such engagements can be a perilous undertaking. While some hackers operate within established legal systems, others exploit vulnerabilities for personal gain.
Organizations must thoroughly vet potential consultants to mitigate the risk of unknowingly engaging with individuals who operate outside legal and ethical guidelines. Furthermore, it is crucial to establish clear goals and constraints at the outset of any engagement with a hacker for hire. Failure to do so can result in unintended repercussions.
- Honesty is paramount in this realm, as both parties should be fully aware of the potential legal and ethical ramifications involved.
- Meticulous research is essential to ensuring that any engagement with a hacker for hire adheres to all applicable laws and regulations.
Securing Your Information in a Dangerous Online World
In today's virtual world, our financial information is constantly at risk from harmful attacks. Cybersecurity experts are dedicated to helping individuals and companies in safeguarding their critical data from these constant threats. A competent cybersecurity expert can establish a multi-layered security infrastructure to mitigate the risk of cyberattacks.
- Installing security updates promptly helps prevent known vulnerabilities from being exploited by attackers.
- Using strong, unique passwords for each account is essential to protect against unauthorized access.
- Be cautious of suspicious emails and links, as they may lead to phishing scams or malware infections.
Take proactive steps to safeguard your information in the digital realm.
Discovering Hidden Risks in Your Systems
In the ever-evolving landscape of cyber threats, organizations must prioritize their security. Penetration testing, also known as ethical hacking, provides a proactive approach to reveal vulnerabilities before they are exploited by malicious actors. By simulating real-world attacks, penetration testers can uncover weaknesses in digital assets and operational processes. This methodology involves a series of controlled tests that emulate the actions of malicious hackers.
Through these simulated attacks, penetration testers gain insight into potential vulnerabilities, allowing organizations to remediate them before they can be exploited by real-world attackers. Meaningful penetration testing delivers invaluable safeguards against a wide range of threats, including data breaches, system compromises, and financial losses.
Building a Cyber-Resilient Future with Ethical Hacking Strategies
In today's interconnected world, safeguarding our digital assets from malicious threats is paramount. Building a robust cyber-resilient future requires a multifaceted approach, and ethical hacking stands out as a powerful tool in this endeavor. By simulating real-world attacks, ethical hackers help organizations identify flaws in their systems before they can be exploited by malicious actors.
Through red team exercises, ethical hackers intentionally probe for security gaps, providing valuable insights into the organization's defense mechanisms. This awareness empowers organizations to strengthen their defenses, implement appropriate safeguards, and ultimately build a more resilient digital environment.
- Ethical hacking plays a vital role in fostering a culture of security within organizations.
- Ongoing ethical hacking assessments help identify and address emerging threats.
- By working together with ethical hackers, organizations can gain valuable expertise and best practices.
 Haley Joel Osment Then & Now!
Haley Joel Osment Then & Now! Neve Campbell Then & Now!
Neve Campbell Then & Now! Alicia Silverstone Then & Now!
Alicia Silverstone Then & Now!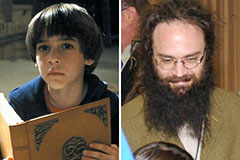 Barret Oliver Then & Now!
Barret Oliver Then & Now!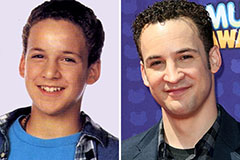 Ben Savage Then & Now!
Ben Savage Then & Now!